
Chinese Cyberspies Deploy New SSH Backdoor to Hijack Network Devices
A new SSH backdoor is being actively deployed by the Chinese cyber-espionage group Evasive Panda (aka DaggerFly) to compromise network appliances. Fortinet’s FortiGuard Labs uncovered the attack suite, named ELF/Sshdinjector.A!tr, which has been used in persistent, covert intrusions since mid-November 2024.
The malware injects itself into the SSH daemon (SSHD), enabling threat actors to establish stealthy, long-term access to compromised devices while executing various malicious actions, including credential theft, system reconnaissance, and remote command execution.
Attack Methodology
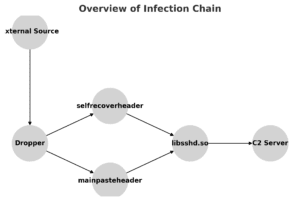
The exact initial access vector remains unknown, but once the attackers breach a device, they deploy a dropper component that:
✅ Checks if the device is already infected.
✅ Ensures the process is running under root privileges.
✅ Drops several binaries, including the malicious SSH library (libssdh.so).
The libssdh.so file serves as the primary backdoor, maintaining Command and Control (C2) communication while enabling data exfiltration and remote control. Two additional binaries, mainpasteheader and selfrecoverheader, ensure persistence on the compromised system.
Capabilities of the SSH Backdoor
Once injected into SSHD, the malware executes 15 powerful commands, including:
🔹 System Reconnaissance – Collects hostname, MAC address, running processes, installed services, and system logs.
🔹 Credential Theft – Reads sensitive user data from /etc/shadow.
🔹 File Manipulation – Lists, renames, uploads, downloads, or deletes files.
🔹 Remote Command Execution – Provides a shell for full command-line access.
🔹 Persistence Mechanisms – Modifies firewall rules, self-recovers, and notifies attackers of malware activity.
Indicators of Compromise (IoCs)
🔻 Presence of unauthorized libssdh.so files.
🔻 Unusual SSH daemon behavior or unexpected network connections.
🔻 Changes in firewall rules or system configurations.
Recommended Security Measures
🔹 Patch & Update Firmware – Ensure all network appliances run the latest security patches.
🔹 Monitor SSH Activity – Regularly audit SSH configurations and detect anomalies.
🔹 Implement Network Segmentation – Limit lateral movement in case of a breach.
🔹 Deploy Advanced Threat Detection – Use security solutions capable of identifying persistent threats.
Conclusion
The emergence of ELF/Sshdinjector.A!tr highlights the increasing sophistication of cyber-espionage tactics used by Chinese APT groups. Organizations must stay vigilant, enforce strict access controls, and monitor network activity to defend against such stealthy, long-term intrusions. Regular system audits and timely security updates remain essential in mitigating these evolving threats.
